Document Library
Listed below, you will find some useful IT support and cybersecurity documents that you are welcome to download and use.

Computers slowing down at the worst possible moment, email systems that behave unpredictably, software no one really understands… and security worries that never quite go away. Law firm owners don’t choose their profession because they love technology. But ignoring the systems that keep your practice running is not an option. Threats are increasing, clients expect more, and the Solicitors Regulation Authority (SRA) assume you’ve done the basics to keep data safe.
Fortunately, good IT doesn’t mean buying the most expensive systems or replacing everything at once. You need to get the fundamentals right to keep your firm secure, make sure your team can work efficiently wherever they are, and have sensible protections in place so a bad day doesn’t turn into a disaster.
Customer Testimonial
“Using the TechStore takes away the hassle and time of managing our IT hardware. Pricing is always
internet competitive, and there is a quick turnaround from order to delivery of equipment, configured and
ready to go. Highly recommend! Mike B (MD)“
You can’t see it. You can’t touch it. But right now, it’s quietly standing between your business and thousands of online threats. Every single email you send, website you visit, or file you download passes through it.
And if it wasn’t there, your business would be wide open to attack.
That invisible protector is your firewall. A firewall is a bit like the security guard at the entrance to your office building. It checks everyone coming in and out, deciding who’s allowed through and who should be stopped at the door.

You know that feeling when you open your inbox in the morning, and it’s already full of junk?
Special offers you never signed up for. “Urgent” invoices from companies you’ve never heard of. Mysterious delivery updates for parcels you didn’t order. Most people sigh, delete, and move on.
But what if one of those emails wasn’t just annoying? What if it was dangerous?
That’s what spam is today. It’s one of the most common ways cyber criminals break into businesses like yours.

An easy-to-follow guide showing you how to choose a new IT support partner. Discover what to look for, what to beware of and the key questions to ask.
The cloud means using powerful computers (called servers) in secure data centres that you access over the internet, instead of relying on the computers and equipment in your office.
Relying on one computer or a single server in the office doesn’t fit how most businesses operate anymore. That’s where the cloud comes in. Just as we moved from paper files to digital files, now we move from digital files stored locally to digital files stored securely online. The cloud gives you the flexibility to access what you need, when you need it, wherever you are.

Like most business owners, you likely have your files stored in several different locations. Some live on your laptop. Some are in a shared folder on the office server. Others are floating around in email threads or saved in someone’s Dropbox or OneDrive.
But when everything is spread out like this, it can be hard to stay organised. People waste time searching for the correct file. Two people accidentally work on different versions of the same document. You’re never quite sure who last updated something.
This is where SharePoint comes in.
You’ve made the smart move and upgraded to Windows 11. Good decision.
And maybe now you’re wondering…
- What’s changed?
- Where do I find things?
- And how can my team get the most out of it without a load of hassle or training?
The good news is Windows 11 is designed to feel familiar, but work smarter. It’s faster, more secure, and packed with features that help people get more done (with fewer distractions). Whether your staff are in the office, working remotely, or constantly on the move, this new system is built to support our modern way of working and to make life easier along the way.

It’s Monday morning. You’re trying to get a quick answer from someone in your business. But they’re working from home today… and your email is sitting in their inbox, unread.
Meanwhile, you’re digging through old email threads to find the latest version of a file. Only to realise someone else has already updated it, and it’s sat in a folder on their laptop. You can’t access it.
Frustrating, isn’t it?
If your business is still relying on spreadsheets, sticky notes or people’s memories to manage passwords, you’re putting EVERYTHING at risk. It’s a bold statement, but it’s true.
Passwords are the keys to your business. And too many companies are still locking their digital front door with a flimsy padlock. Here’s a reality check:
Globally, a staggering 30% of people reuse the same passwords across multiple accounts.
That means that if one password gets leaked or hacked, attackers could potentially gain access to everything. From your emails and cloud storage to client data and bank account.

For the owners of many small and medium-sized businesses, IT can feel like a necessary evil. It’s the stuff you call someone about when it breaks. The Wi-Fi goes down. An email account gets hacked. The printer stops talking to the laptop… Cue the panic. Then the phone call. And then the invoice. Sound familiar?
If your business is still running on Windows 10, you’re officially running out of time.
It reaches end-of-life on 14th October, which means the end of Microsoft’s free support. There will be no more security updates, bug fixes, or technical help if things go wrong.
Still think you can put off upgrading? Think again.
Cybercriminals love outdated software. They know businesses delay upgrades and leave themselves vulnerable. Without security updates, Windows 10 will become a prime target for malware, ransomware, and data breaches—risks that could cost your business thousands or even put you out of action.
As business owners, we do everything we can to secure our businesses. We invest in security tools, and train our teams
to spot scams and stay alert to threats.
But here’s the uncomfortable truth: No system is ever completely safe from attack.

Cyber Essentials represents the UK Government’s minimum baseline standard for cyber security for organisations of all sizes in the UK. The annually renewable certification scheme is aligned with five technical controls designed to prevent the most common internet-based cybersecurity threats.
Cyber Essentials certification demonstrates that an organisation is protecting itself by implementing the most critical cybersecurity controls. A team of experts regularly reviews the scheme to ensure it stays effective in the ever-evolving threat landscape.
Cyber Essentials certification includes automatic cyber liability insurance for any UK organisation that certifies its whole organisation and has less than £20m annual turnover. At the first level of Cyber Essentials, organisations assess themselves against five basic security controls, and a qualified Assessor verifies the information provided.
All the self-assessment questions are available to download for free in advance. Once you have passed Cyber Essentials, you can apply for Cyber Essentials Plus, which is a hands-on audit of your systems. Read on for more info.

Artificial intelligence (AI) is no longer something that will “arrive in the future”. It’s here to stay, and it’s transforming the way businesses work today.
Microsoft’s AI-powered assistant, Copilot, is already helping businesses to streamline processes and save time. And with Wave 2 rolling out, Microsoft’s taking things to a whole new level – helping you supercharge productivity, collaboration, and decision making. What does this mean for your business? Let’s look at how you can make the most of these updates.
Whether it’s the familiarity of your phone’s setup or the custom keyboard shortcuts on your laptop, there’s something comforting about using a device you know inside out.
Let’s face it, everyone loves their own gadgets. It’s one of the reasons many businesses are hopping on the Bring Your Own Device (BYOD) bandwagon, letting employees use their personal devices for work. It’s a win-win, right? Employees stay in their comfort zone, and businesses save on tech costs.
Well, not so fast.
Allowing personal devices into the workplace isn’t as simple as it sounds. Sure, it can boost productivity and morale. But it also opens a Pandora’s box of security risks, compatibility issues, and potential headaches.
Your team is juggling emails, managing client files, hosting online meetings, and working from different devices. Everything seems fine…
…until one day, an employee clicks on a suspicious email link. Suddenly, your files are locked in a ransomware attack…
Or maybe you find out an ex-employee’s login still works, and they’ve been snooping around…
Or your team’s devices are so out of sync that half your staff can’t access the tools they need remotely.
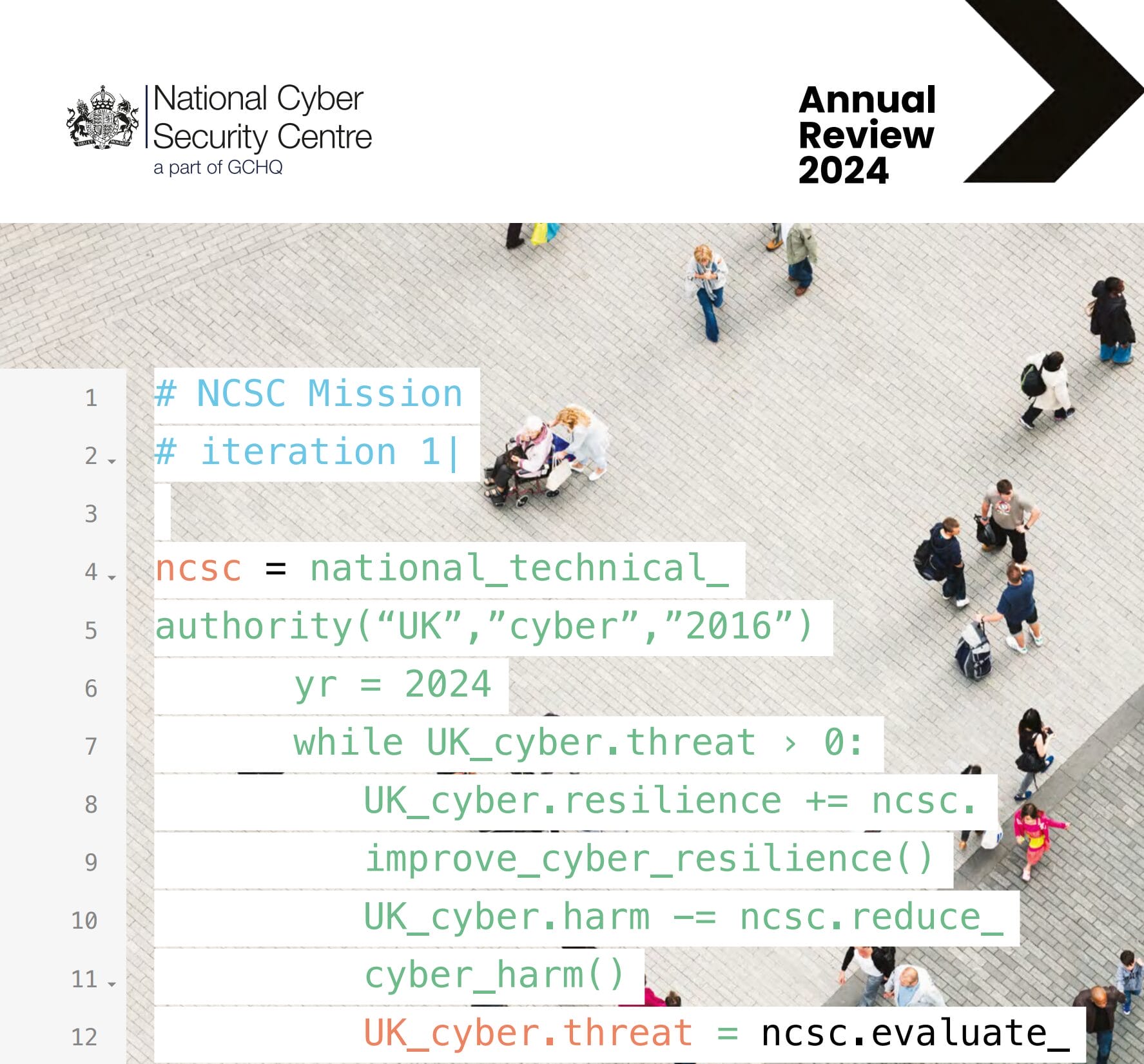
Cyber now underpins every aspect of everyday life. It is central to our economy and society, offering huge potential for the Government’s number one mission for growth and prosperity. But alongside its huge benefits there are also risks and vulnerabilities, making it more important than ever that we secure our online world.
The Government has taken a number of steps to strengthen our national security in the cyber realm, but we can’t
do it alone. We need businesses and other organisations to boost their own cybersecurity where they can. While
we have made significant progress, this report shows that the cyber threat is dynamic and grows more complex each year.
As this report shows, while AI presents huge opportunities, it is also transforming the cyber threat. Cyber criminals
are adapting their business models to embrace this rapidly developing technology – using AI to increase the volume and impact of cyber attacks against citizens and businesses, at a huge cost. Meanwhile the proliferation of advanced cyber intrusion tools is lowering the barrier for entry to criminals and states alike.

It’s Monday morning and your team is getting ready for another busy week. But then the inevitable happens. Your internet connection seems to be on a coffee break, and half the team is sitting idle, waiting for their computers
to wake up from their morning nap. Sound familiar?

You’re running your business, and your day starts like any other. You check your email and find an urgent request from a key client. It has their usual email signature at the bottom.
You follow their instructions… only to realise later that the email was a sophisticated scam. The email signature, so familiar and seemingly reliable, was expertly forged. The damage is done, and you’re left wondering how you could have been so easily deceived.

All businesses face a growing number of cyber threats. Cyber criminals no longer focus solely on large corporations; they’ve realised that small and medium sized businesses can be easy targets due to limited resources and lack of stringent security measures. One of the most important ways of defending against attaclks is to train your users.
Imagine this: You arrive at your office on a seemingly ordinary Monday morning, ready to tackle the week ahead. But as you power up your computer, you’re greeted not by the familiar hum of productivity, but by… nothing.
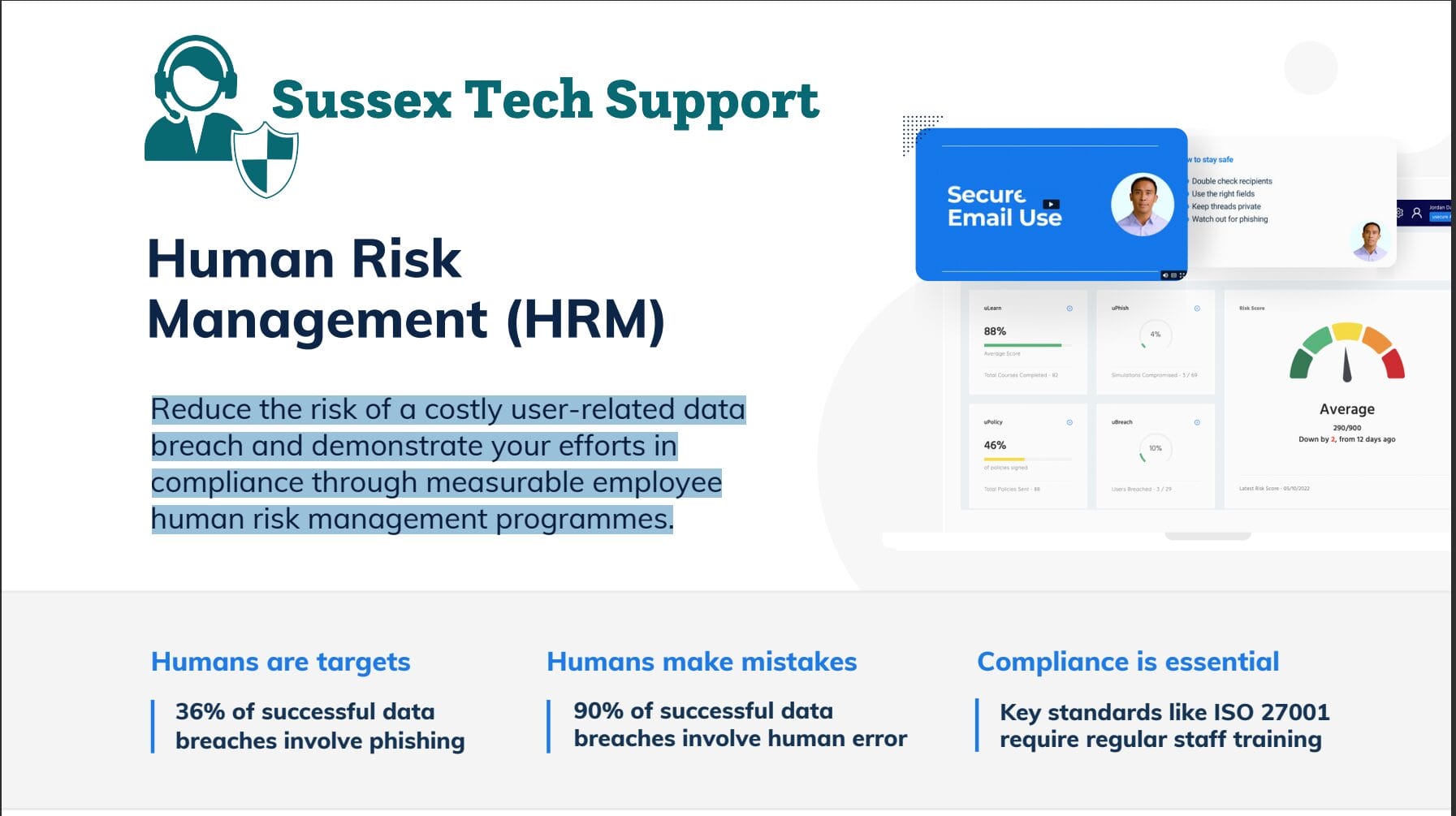
Reduce the risk of a costly user-related data breach and demonstrate your efforts in compliance through measurable employee human risk management programmes.

By reading this, you probably already know the importance of having solid cyber security measures in place. Hopefully, you’ve got protections such as firewalls, antivirus software, and multi-factor authentication (where you get a login code from another device). Great work!
But here’s the thing: No matter how many security measures you have in place, there’s always a chance – however small – that someone might breach your defences. No system is 100% foolproof.

This guidance has been jointly developed by the insurance industry bodies ABI, BIBA, IUA and the NCSC. It is for organisations experiencing a ransomware attack and the partner organisations supporting them. It aims to minimise the overall impact of a ransomware incident on an organisation and help reduce:
- disruption and cost to businesses
- the number of ransoms paid by UK ransomware victims
- the size of ransoms where victims choose to pay

Imagine this: You’re sitting in your office, sipping your morning coffee, going through your emails. Everything seems routine until you stumble upon an alarming message from your bank.
You click the link and log in to your bank… but something feels wrong.
You go back to your email and look again. Your heart skips a beat as you realise it’s not from your bank at all… it’s a cleverly disguised phishing scam.

Data is the lifeblood of your business. That might sound dramatic but think about it for just a moment. It’s everything from customer profiles and financial transactions to confidential business plans and intellectual
property.
Realistically, your success and reputation hinge on how well you protect your data. Why does it need protecting? Every day, your employees access and share sensitive information across various devices and networks. And while this connectivity boosts productivity, it also exposes you to bad people with a common goal: They want to steal as much of that data as possible.
That’s where encryption comes into play.

How Can Copilot 365 help ‘YOU’ with your work when using Microsoft Applications? What this selection of videos and see how.

Microsoft Teams Phone is rapidly becoming the go to solution for businesses looking to simplify their communications, and Operator Connect is the perfect addition to enhance your Teams experience. With its seamless integration, Operator Connect streamlines your Teams calling capabilities and maximises your return on investment.

Horizon sits in the cloud. This vastly increases the capabilities, improves the reliability and customer experience of your business. Horizon allows your business to optimise your business investment, improve your customer satisfaction, retain talented staff and save time and money.
Most businesses have seen their technology needs develop fast. These needs are still accelerating – and will continue to do so throughout this year and next. It’s important that you have a technology strategy to drive this and a support partner rather than just a policy of reacting to needs as they arise.
This guide helps you select the IT support and security partner that’s right for you. And we mean partner. Not an IT support company. Not just an IT support provider, but a partner that takes your
business as seriously as they take their own.
In the last 12 months, 39% of businesses and 26% of charities reported having a cyber breach or attack. To help you minimise the impact of a cyber attack, the Cyber Resilience Centre have created a Cyber Incident Response Plan for you to use.
The cyber security incident response plan provides you with a process that will help your business to respond effectively in the event of a cyber-attack. Therefore, we highly recommend downloading this plan and reading it so you know what to do if a cyber-incident happens in your business.

You can’t fail to have noticed that cybercrime and cyber-attacks are becoming more common. Every day, you will see new headlines about data breaches, hacking, cyber-attacks, and various forms of crime. As a result, over half of the small and medium businesses have reported being the victims of cybercrimes.
The Sussex Tech Cybersecurity Essentials booklet takes you through all aspects of cybersecurity. The information it contains shows you how to best secure your business against a wide variety of cyber threats.